A French hacker, who goes by the name of Maximehip, has just released a good few exploits for Apple’s operating systems. Here’s all you need to know about it.
Table of Contents
Phoenhex Dev Team Releases Safari Exploits
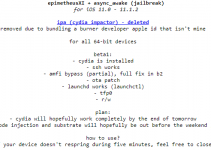
Exploits for the Safari web browser on iOS 10.3.2 and macOS 10.12.4 have just been released. These new exploits are the brainchild of Phoenhex Dev Team, of which Maximehip is a part.
Here are the details of all security vulnerabilities –
- CVE-2017-2533
- CVE-2017-2535
- CVE-2017-2534
- CVE-2017-6977
This exploit is of not useful for macOS but has huge practical importance for jailbreakers. A skilled hacker can utilize them to run unsigned code from Safari (JailbreakMe).
Why is a Safari Exploit important?
A Safari exploit is of immense importance. According to the CVEs given above, there’s a high probability that this exploit might work on previous iOS versions as well. If it works on iOS 10.2, iPhone 7 and iPhone 7
If it works on iOS 10.2, iPhone 7 and iPhone 7 plus will certainly get a jailbreak. This exploit, when combined with extra_recipe, will be able to jailbreak those devices.
This exploit is Safari exploit, not a WebKit exploit. It doesn’t grant you remote code execution, only local code execution.
This means the malicious/jailbreak code will need to be executed locally on your browser.
Is a Safari exploit enough for a 10.3.2 jailbreak?
Unfortunately, the answer is no because a Safari exploit is just one of the many parts of the jailbreak puzzle.
This exploit is just a Sandbox escape and hence can’t be used to develop a jailbreak tool alone. We will still need other exploits along with this to gain root access.
Once a hacker gains root access, he can then develop a working jailbreak tool for the average user.
If a jailbreak based on this exploit materializes, it would function exactly like Luca Todesco’s JailbreakMe9 Safari jailbreak. Now only if someone could combine this exploit with Adam Donenfeld’s exploits.
Jailbreak or no jailbreak – this is still a huge development in itself. Exploits are getting scarce by the day so kudos to Phoenhex Dev Team for finding them.
Don’t forget to save your SHSH Blobs just to stay on the safe side. Here are a few tutorials you can follow –
- TSS Saver Tweak – One-click tool to Save SHSH Blobs
- How to Save SHSH2 Blobs for iOS 10.2.1/10.3/10.3.1
- How to Save SHSH Blobs with Telegram Jailbreak Bot
For more scene updates, follow us on Facebook and Twitter.