A new WiFi vulnerability called “WiFiDemon” allows hackers to infect iPhone and iPad devices wirelessly. Here’s all you need to know about it.
Table of Contents
What is WiFiDemon?
Discovered by the ZecOps Mobile Research team, WiFiDemon is a new “zero-click” WiFi bug that allows an attacker to infect vulnerable Apple devices.
This vulnerability requires absolutely zero interaction on the part of the user. The attacker only requires the victim to have WiFi enabled to trigger malicious code.
wifid (WiFi daemon) is an important system daemon responsible for handling WiFi connection. Tampering with “wifid” could possibly lead to a full system compromise.
Hackers can use the WiFiDemon vulnerability to perform two kinds of attacks:
- Zero-click Attack: The zero-click attack requires the WiFi to be set to Auto-Join, the default option on iOS. It affects iOS 14 operating systems beginning from 14.0 to 14.3.
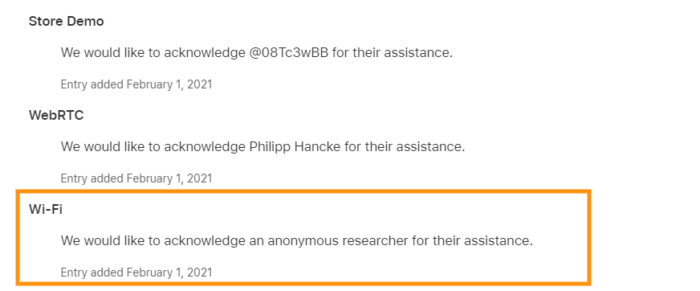
Apple patched this bug in the iOS 14.4 update. The security notes credit an “anonymous researcher” and do not list a CVE, which is surprising for such a potent bug.
- Zero-Day Format Strings Attack: The format strings attack is an RCE (Remote Code Execution) bug that only requires the user to connect to a malicious wireless network. As of this writing, iOS 14.6 is vulnerable to this attack.
Interestingly, this bug can be used to develop a partial sandbox escape locally for jailbreaking.
How can I protect my iPhone/iPad from WiFiDemon?
This vulnerability is only “partially” patched. So, you cannot protect your device from the “format strings” attack.
However, you can take a few precautions to protect your device from a zero-click attack.
Method 1
Since this bug affects iOS 14.0-14.3, you can keep your device protected by simply upgrading to iOS 14.4 or above.
We suggest updating to iOS 14.6 firmware – the current stable release.
If you are a jailbreaker, do not update your device just yet and wait for a jailbreak-centric patch to drop.
Method 2
Disable the WiFi Auto-Join Feature, which is enabled by default on all iOS devices.
Open the Settings app and go to WiFi > Auto-Join Hotspot and select Never.
Method 3
Do not join unknown WiFi networks, especially public networks. You never know who might be operating it behind the scenes.
For more iOS security news and updates, give us a follow on Twitter and Facebook.