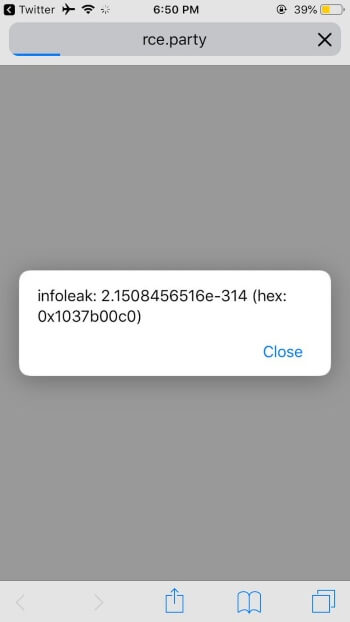
Luca Todesco, the developer behind Yalu jailbreak, demonstrated yesterday a Safari proof-of-concept exploit for iOS 13 Beta 3. Check out the full exploit below.
Table of Contents
Luca Todesco demonstrates iOS 13 Safari bug
Once again, Famed developer Luca Todesco has successfully pwned Apple’s latest operating system while it’s still in the beta development stage.
This time around, it’s Safari’s WebKit engine that has been exploited by the young hacker.
According to Todesco, this exploit is based on the “Structure::create should call didBecomePrototype()” WebKit bug.
in case you don't have a jsc shell handy, https://t.co/sURyuUukbC! even works as recently as iOS 13b2
— qwertyoruiop (@qwertyoruiopz) July 6, 2019
You can access the proof-of-concept webpage on rce.party/wtf.html if you have a compatible Apple device running iOS 13 beta 3 firmware or below.
Since the exploit is based on WebKit, you must use the stock Safari web browser app.
Amy of RET2 Systems wrote a full-blown exploit for iOS 12.3.1 based on Luca’s proof-of-concept.
The security researcher also uploaded a video on her Twitter account demonstrating SOP (Same Origin Policy) bypass via arbitrary read/write.
Decided to take @qwertyoruiopz's nday and write a full exploit for it. Here is a exploit for iOS 12.3.1 doing SOP bypass via arbitrary read/write pic.twitter.com/VH6ah7UNot
— itszn (@itszn13) July 6, 2019
Compatibility
Luca has confirmed that this exploit is fully functional on iOS 13 Beta 2 firmware.
Some users who opened the aforementioned webpage via Safari also confirmed that the exploit is working just as expected on iOS 13 Beta 3 and below.
However, we couldn’t get it to work on a device running iOS 12.1.3 even after multiple attempts.
Where does this leave us?
Unfortunately, developers will not burn a functional exploit on an outdated version such as iOS 12.1.3 or 12.2.
In spite of that, developers are making good progress, which could result in a full-blown jailbreak within a few months from iOS 13’s public release.
Using Luca’s exploit, renowned hacker Ben Sparkes has also achieved root shell access on iOS 13 Beta 3.
got shell btw pic.twitter.com/6IEhgkFDPp
— sparkey (@iBSparkes) July 7, 2019
Furthermore, it’s highly unlikely that Apple will patch private exploit that’s still in the hands of hackers. So, staying on the lowest firmware, although recommended, will likely yield no dividends at all.
Which iOS version are you going to stay on? Leave your replies below.


I know it’s not the right page, but can you tell me if it’s possible to go back to 12.1.2 from 12.3 please, having the ssh certificates saved and how to do it?
Unfortunately, the phone has looped over me to restore the IOS 12.0 backup and I could do nothing but restore to 12.3 🙁
Sorry, it’s no longer possible.
And at 12.2?
Not possible since there’s no nonce setter available for your current version.