Security researchers at Versprite recently reported a new vulnerability in AirMail 3 that could allow a hacker to obtain a copy of all emails almost instantly.
Table of Contents
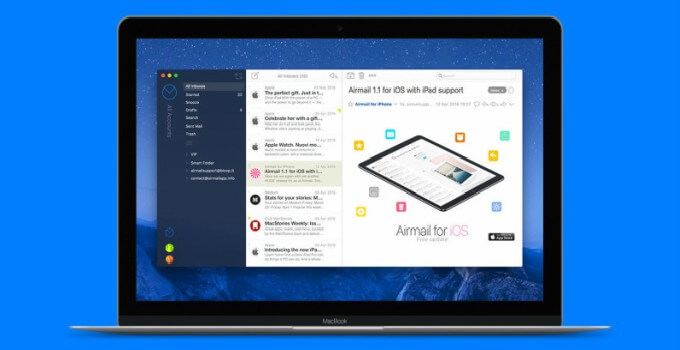
Vulnerability discovered in Airmail 3 mail client for macOS
Airmail 3 is a popular alternative for sending and managing e-mails on macOS. As its user base increases, the macOS mail client is increasingly becoming a target for hackers.
In order for a hacker to obtain a copy of all emails sent or received via Airmail, the user must open an email that the hacker sends him with a malicious link. The phishing e-mail can then trigger commands in the mail client that can forward e-mails to other addresses.
In some cases, the researchers managed to trigger the exploit without forcing the user to click a link.
According to VerSprite experts, the app uses a custom URL scheme called airmail:// that can be used to autonomously send emails with attachments.
These attachments may be additional emails, email attachments, or even the entire database content with all the emails.
Since the app stores data in the same location, it’s easier for an attacker to determine where the files are stored on the target system.
How can you stay safe?
Although this exploit is powerful, it can be difficult for an attacker to get hold of your emails if you are smart.
Firstly, the attacker must ascertain that the target uses the AirMail mail client on Mac. Secondly, the user must deliberately open the link in the fake phishing email.
Until the developers patch this vulnerability, stay on your guard. Here’s what all Airmail users should do right now –
- Steer clear of suspicious messages that include links to external websites. A single click can cause all your personal data to go into the wrong hands.
- Disable HTML content in emails and stick to the text version.
- Change the default signature of the app.
(Source – VerSprite)