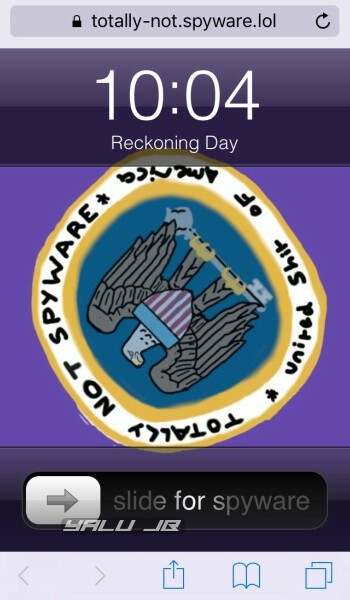
Ben Sparkes recently released totally-not.spyware.lol JailbreakMe out of the blue. While this jailbreak lets users jailbreak their devices without a computer, it also exposes them to WebKit attacks.
Table of Contents
iOS 10-11.3.1 users are vulnerable to Safari exploit
Two months ago, Phoenhex Dev Team released the pwn.js exploit for mobile Safari web browser. As expected, Apple promptly patched this vulnerability in iOS 11.4 firmware.
Jailbreak developers pounced on the opportunity and quickly developed a browser-based jailbreak for iOS 10-10.3.3. However, in doing so, the team left all jailbreak-able versions vulnerable to web attacks.
According to Jake James, all devices running iOS 10-11.3.1 are vulnerable, even though the jailbreak works only support iOS 10.
James also developed a proof-of-concept that transforms totally-not-spyware into a real spyware using eggshell.
Make no mistake – Spyware JailbreakMe itself is secure but creators of other websites may have sinister intentions.
An attacker could slap up a pwn.js-based malicious website, spread the link, and gain remote access to users’ devices on the affected firmware.
When will a security patch be released?
Back in 2016, security researcher Luca Todesco developed JailbreakMe 4.0 for iOS 9 firmware and immediately released a patch for his exploit.
At the time of this writing, Ben Sparkes and his team are working on a similar security patch for affected versions. This upcoming patch will likely be distributed in the form of a tweak via Cydia.
As of right now, there’s no fix except for upgrading your device to iOS 11.4 (final) or above versions.
Alternatively, you can disable Javascript from Safari’s settings. Doing so will render this WebKit vulnerability useless. However, it’s not a feasible solution by any means; the reason being that every website uses Javascript technology in some capacity.
With that being said, Phoenhex Dev Team member Niklas Baumstark has close-sourced the stage 2 of pwn.js exploit to protect users from malware. Nevertheless, a full-blown security patch would still prove useful.