A group of security researchers has released an iPhone exploration toolkit. Here’s all you need to know about it.
Table of Contents
What is objection?

- Explore the filesystem
- SSL pinning bypass
- Class method monitoring
- Dump process/module memory
- Interact with iOS keychain
- Bypass TouchID
- Monitor iOS pasteboard
- Extract iOS binary cookies
Here are the slides by r0 Crew, which explain how objection works.
Remember, this is not a jailbreak and will not allow you to run Cydia on your iPhone. This tool is developed specifically for hackers and jailbreak developers.
How objection works
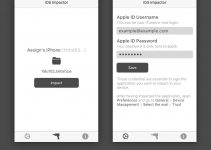
This toolkit is based on Frida and works only with the iOS operating system at the moment.
Android is also compatible with this toolkit but it is yet to be fully ported to Google’s mobile operating system. Here’s a brief description of how it works.
- Objection injects objects into a patched IPA during runtime.
- It then executes them within the application’s sandbox.
- A hacker can now perform all actions given above such as browsing the iOS filesystem from the app.
- You can also download and upload files if you have necessary permissions to do so.
Why is it important?
iOS jailbreaks and exploits are getting increasingly rare to come by with each new firmware Apple rolls out. This severely limits the ability of hackers to poke around with iOS.
Usually, hackers need to develop a sandbox escape to perform this level of research. But things are changing with the release of this amazing utility.
Any jailbreak developer can now easily perform routine security assessment without having a sandbox escape or root access. This will lead to more and better exploits being developed in the future.
For more iOS security updates, subscribe to us on Facebook and Twitter.