Hacker AppleDry05 has successfully gained root privileges on Apple’s latest operating system – iOS 14. Here’s all you need to know about it.
Table of Contents
AppleDry05 achieves Root access on iOS 14
Bas Van Turnhout aka AppleDry05, the developer behind FilzaEscaped utility, has achieved root access on the iOS 14 operating system.
For the uninitiated, getting root access on iOS simply means gaining administrator privileges to the device.
By default, the user of a device is called “mobile” and has restricted access to the system. Once you gain root access, you can bypass this limitation.
Check out the video demonstration of the iOS 14 root access bug below.
Root access achieved on iOS 14 🔥🔥🔥. It could be developed as a full-blown iOS 14 jailbreak in the future (dev – @AppleDry05). #RETWEET for visibility
. pic.twitter.com/9gSbustKPg— Yalu Jailbreak (@Yalujb) July 18, 2020
In this short video, the developer is seen logging in to the Terminal as “root” on his iPhone 6S using Shelly SSH client. He then proceeds to use the following commands as root:
- uname – The “uname” command displays the hardware and software information about the device.
- ls – The “ls” command lists the name of files in a specific directory.
Unfortunately for us, the developer has not been online since yesterday. So, we do not know which devices are affected and to what extent.
If this bug works on A12/A13 devices, this will be a groundbreaking discovery that could pave the way for the development of iOS 14 jailbreak.
Could this bug lead to an iOS 14 jailbreak?
Apple has changed a lot of stuff in iOS 14, which poses a host of challenges to developers – especially on the security front.
For instance, the Objective-C runtime runs differently on iOS 14 as compared to its predecessor – iOS 13.
If rumors are to be believed, Apple has also patched checkra1n to some extent on devices having the A10 or A11 system-on-chip. Apple’s latest operating system restricts access to the user partition if the device boots up using DFU mode.
This lends credence to the fact that this is indeed a new exploit, which has not been released in the public domain yet.
If the root access bug does indeed rely on checkm8 exploit, then there’s no point in developing a “full jailbreak”.
The checkra1n development team has confirmed that it plans to release an update to checkra1n with iOS 14 support. Since checkra1n is based on the checkm8 exploit, it will end up supporting the same devices anyway.
checkra1n jailbreak on iOS 14
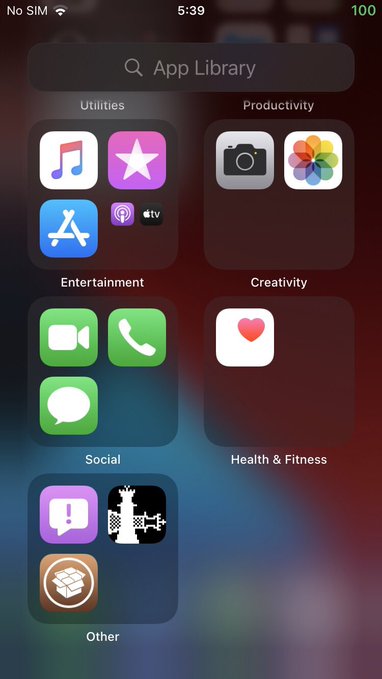
While gaining root access is a great achievement for developers, it doesn’t offer much to the average jailbreak user. Sure, you can install FilzaEscaped on your Apple device… but that’s about it.
To run Cydia tweaks, you also require an AMFI/CoreTrust bypass that allows unsigned code execution.
What do you think about this new root access bug? Is it based on checkm8 or will it lead to jailbreak in the near future? Let us know your thoughts in the comments section below.