iOS 9’s BootROM and iBoot source codes have been floating around for some time now. Thankfully, a Twitter user managed to get his hands on them and leaked it to the public.
Table of Contents
q3hardcore leaks BootROM and iBoot source codes
A Twitter user who goes by the name, q3hardcore, recently leaked Apple’s classified internal code online.
Earlier, this code was shared by developers in private and even sold by some before it was leaked. It has been in the public domain for about 4 months.
The source code package titled iBoot_BootROM_iBSS_iBSS_iLLB_Source_Codes.rar is available for download publicly below. This version is missing a few files that were present in the original leak.
It also includes a “Documents” section, which provides a lot of in-depth information on how various components work.
This source code pertains to a specific build of iOS 9 firmware (9.3.x). As far as the device-specific code goes, there are identifiers present for iPhone 6s/6s plus, and iPhone SE.
Download BootROM/iBoot source code
- RAR archive (mirror)
How can this prove useful?
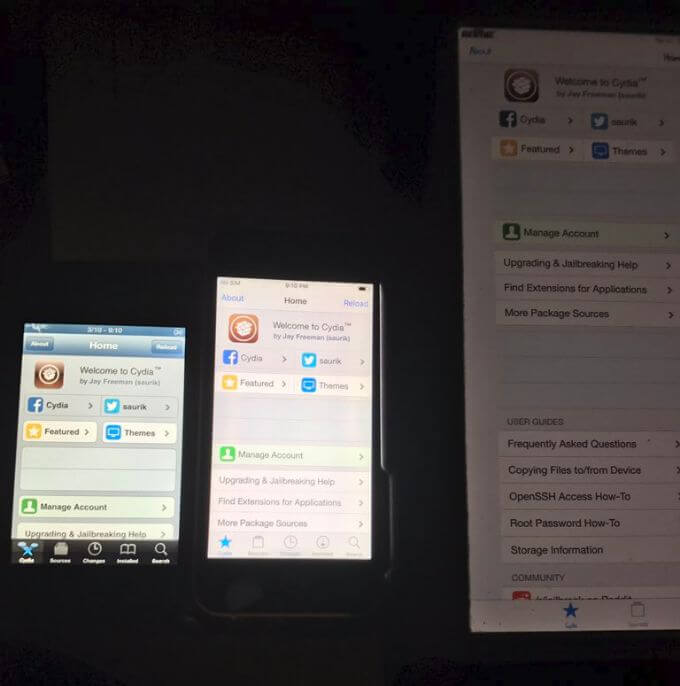
Untethered jailbreak for iOS 9
An iBoot exploit could potentially lead to an untethered jailbreak for the affected iOS 9 versions.
This seems somewhat plausible because an iBoot exploit is relatively easier to build.
Downgrade without SHSH
An untethered downgrade requires a BootROM exploit, which is very valuable and difficult to develop.
Even if a hacker releases such an exploit publicly, it will only be useful for 32-bit devices.
64-bit devices require a much powerful exploit for downgrading because they have SEP firmware to take care of.
Security research
Such a leak is of immense importance for professional security researchers and jailbreak developers alike.
Hackers can’t compile or test this code out because of missing tools. They can, however, use it to find security vulnerabilities in iOS 9 and then develop exploits based on them.
Moreover, it can also prove useful for finding vulnerabilities for future versions and modern 64-bit devices.
As you already know, a BootROM exploit allows users to downgrade without SHSH Blobs. This is essential




![How to Downgrade iOS 10.3/10.3.1 to iOS 10.2.1 [iPhone/iPad/iPod] How to Downgrade iOS 10.3/10.3.1 to iOS 10.2.1 [iPhone/iPad/iPod]](https://cdn.yalujailbreak.net/wp-content/uploads/2017/03/image-2017-03-27-2-211x150.jpg)
Hardcore Fuck Days Coming for Apple Soon in the Future… I can smell it…
Link not working
I will update the link, just wait.
Thanks for the upload! Will use for research purposes.
Welcome.
Link not working
I have updated it.
Please re-upload the download link!
ditto on that
This is awesome!