powend exploit achieves sandbox escape and privilege escalation on iOS 12.1.4 and older firmware. Here’s all you need to know about it.
Table of Contents
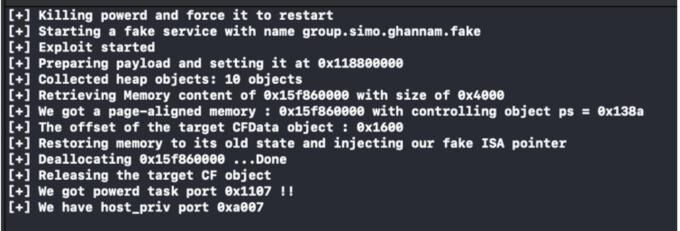
How powend exploit works
powend is an iOS exploit based on a powerd vulnerability that achieves sandbox escape and privilege escalation on iOS 12.1.4 and below.
Hacker Mohamed Ghannam of SSD Secure Disclosure first discovered this vulnerability at the Hack2Win Extreme competition. The hacker went on to win the iOS Privilege Escalation category at the TyphoonCon hacking conference 2018.
The security vulnerability (CVE-2019-8549), which was patched in iOS 12.2, lies in the “powerd” daemon in the iOS mobile operating system.
Hackers can utilize it to gain arbitrary address reads with an unlimited amount of memory and arbitrary address deallocation with arbitrary size, which ultimately leads to Sandbox Escape.
And, what’s more, it doesn’t just provide Sandbox Escape, it also grants you root user privileges, which can be used to call kernel APIs that are reserved for processes running as root.
This will increase the attack surface available to the hackers and leave the iOS kernel even more vulnerable.
Can powend lead to a jailbreak?
Sandbox escape, while an important component of a jailbreak, doesn’t give you root access to the filesystem or exploit the kernel.
Further, it has a major compatibility issue in that it only supports devices without the A12 Bionic processor.
Therefore, iPhone XS (Max) and iPhone XR devices, which still don’t have a full jailbreak, will remain invulnerable to this exploit.
All things considered, it can allow a jailbreak developer to update or develop from scratch a new Houdini-style semi-jailbreak application for iOS 12.0-12.1.4.
Applications like FilzaEscaped and GeoFilza may also receive an update somewhere down the line provided more research is done on this exploit.
For more iOS security news and updates, follow us on Facebook and Twitter.