Kim Jong Cracks team is back at it again! Team member Kevin Bradley aka nitoTV has just demonstrated a SEPROM exploit on checkra1n jailbreak.
Table of Contents
nitoTV demonstrates SEPROM exploit on checkra1n jailbreak
Kevin Bradley aka nitoTV has demonstrated SEP exploit on a checkra1n-compatible device.
Although Kevin is an Apple TV expert, he also teases vulnerabilities and exploits on iOS devices occasionally.
The hacker posted the following image on his official Twitter handle to demonstrate SEPROM exploit on checkra1n.
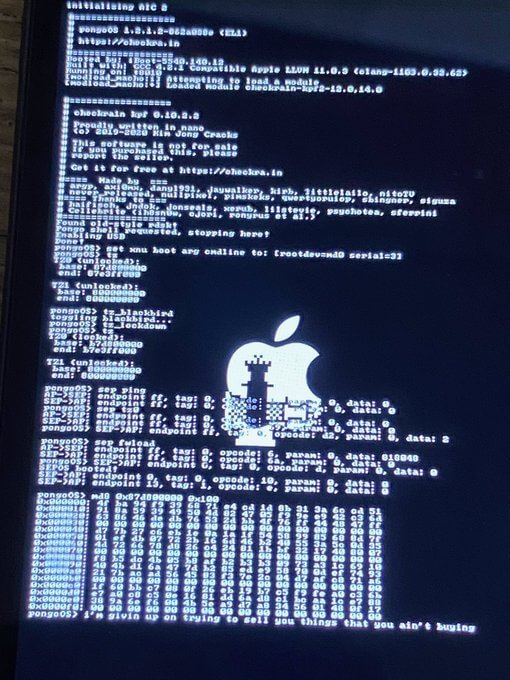
SEP exploit on checkra1n jailbreak
Apparently, A7 and A11 devices are not vulnerable to this exploit (yet), possibly because of a difference in the way they access the TZ0 register.
Nevertheless, it’s possible to make the exploit work on A7/A11 devices since these devices are “technically” vulnerable.
On the other hand, devices with A8, A9, or A10 system-on-chip are vulnerable. However, A10 devices are somewhat limited at the moment.
Security Implications of a SEPROM exploit
1. Downgrades to unsigned operating systems
Up until now, downgrading iOS was not possible due to SEP restrictions. With a SEP exploit, we can load or flash an unsigned firmware on our device.
Back in the day, downgrades with SHSH Blobs would not work because the SEP firmware was incompatible with older iOS firmware. iOS would fail to boot if the iOS version doesn’t match the SEP version.
We can now downgrade (tethered) devices with the A8/A9 system-on-chip to unsigned iOS versions. Devices with the A10 system-on-chip, on the other hand, will still require SHSH Blobs for downgrades.
All in all, you can install any compatible firmware on an affected device using SHSH Blobs.
If you don’t have SHSH Blobs, you can still install any compatible firmware but it would stop working on a reboot unless you run checkra1n jailbreak again.
2. Dual-Boot
Dual-booting allows you to have the best of both worlds. You can run a secondary iOS version of your choice while keeping the primary version intact.
However, you will only be able to use the secondary operating system in a jailbroken state.
The checkra1n development team might incorporate this exploit in the next update of checkra1n. It will most likely be optional and the tool will allow users to opt-out due to security reasons.



