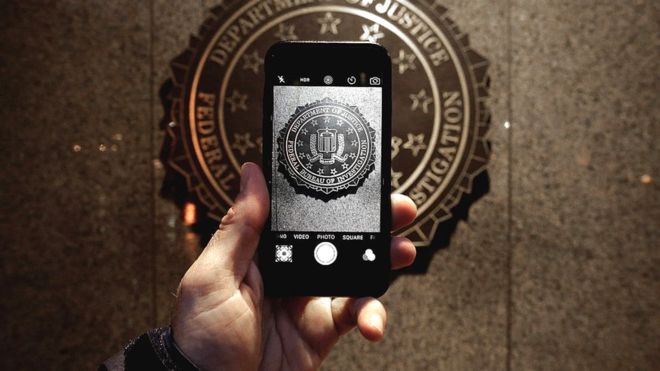
It is not known yet how the FBI went about cracking that dreaded iPhone 5C. FBI received the help of a third party company called Cellebrite.
Cellebrite specializes in data mining and retrieval. 900 GB of data was leaked last month from Cellebrite’s servers. According to the hacker that snooped on their data, they stole exploits from the jailbreak community.
The information from this leak reveals that Cellebrite had sold its technology to many countries such as Russia, Turkey and the United Arab Emirates.
Cellebrite markets a turnkey solution – the Universal Forensic Extraction Device (UFED). It is a box that can retrieve SMS, emails and all kinds of data from hundreds of smartphones as well as older iPhone models. The latest devices have security mechanisms that are harder to hack into.
After recovering and decrypting the data, the hacker gave some additional information too. Cellebrite’s iOS hacking code resembled the exploits used by jailbreak developers. Jonathan Zdziarski, a well-known security researcher confirmed that the iOS files used by Cellebrite to break into the iPhone were identical to jailbreak tools.
One of the configuration files contained a reference to limera1n, a jailbreak software developed by hacker Geohot, and QuickPwn. The code was modified to fit the needs of FBI investigators. There is also presence of a code that lets you obtain password to unlock an iPhone by brute force technique.
They have surely used code from jailbreak tools in their products. This means they have stolen software from the jailbreak community and hence can be sued. In their defense, they said they are always researching and using information from the security community.
Cellebrite spokesperson also told that the technology developed by the company is used in cases of child trafficking, assaults, murders, etc. Given the profile of some of the company’s clients such as the authoritarian regimes mentioned above, UFED is certainly also used for surveillance, hacking and sabotage.
They have got bad press following this incident. The company also tried to downplay the data theft from their servers by saying that it contained only “basic information” such as contacts of its customers and nothing important.