After an excruciating dry spell of months of getting no exploits, we finally have something to look forward to. Zimperum zLabs has just released a new exploit for iOS 11.2.2 and older firmware versions.
Table of Contents
Zimperium zLabs Team releases Sandbox Escape PoC
Israeli Security researcher Rani Idan has just published a detailed write-up of his iOS 11.2 vulnerability.
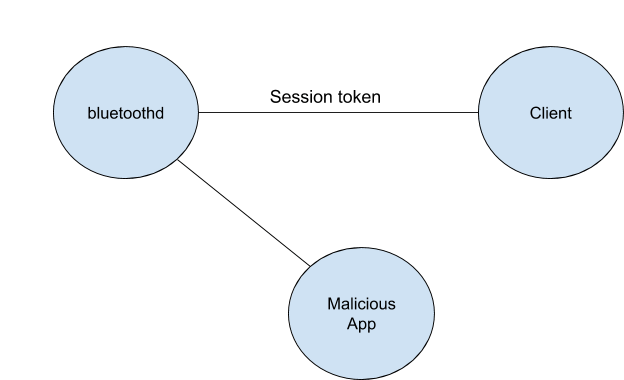
This proof of concept exploits a vulnerability in the bluetoothd daemon of iOS 11.2.2 firmware. Although this proof of concept pertains to the bluetoothd daemon, it can be applied to several other daemons as well.
Here’s a simplistic explanation of how this proof of concept works –
- A client communicates with the bluetoothd daemon starts a session.
- Hacker targets the daemon through a malicious application and brute-forces the session token.
- The malicious application then adds callbacks to the client process.
- This allows the hacker to gains the necessary permissions to escape the sandbox.
Which versions are compatible with this vulnerability?
Since Zimperium is a legitimate security company, it always sends the vulnerabilities to the respective device manufacturers.
In this case, they already sent the vulnerability to Apple so they could promptly patch it. Surprisingly, Zimperium zLabs discovered this vulnerability back in November 2017.
Apple fixed vulnerabilities CVE-2018-4087 and CVE-2018-4095 in iOS 11.2.5, tvOS 11.2.5, and watchOS 4.2.2 in January 2018, two months after its discovery.
Therefore, you can only utilize it on iOS 11.2.2 and below versions.
According to Idan, Apple’s patch isn’t up to par, which leaves room for further exploitation.
Can this lead to an iOS 11.2.2 jailbreak?
Considering this is a proof of concept and not a proper exploit, I believe not much will come of it.
However, we can still get an iOS 11.2.x port for semi-jailbreak applications such as Houdini and Torngat.
A new version of Electra jailbreak is pretty much out of the question at this point in time.
With that said, any progress is good progress and this will allow other hackers and jailbreak developers to continue their research on iOS 11.2.x firmware.
Are you sitting tight on iOS 11.2 and above versions? If yes, leave your comments below.
For more security community news and updates, follow us on Twitter and Facebook.




Sir my iPhone X update iOS 11.2 and I love JB but ?????
Please sir iOS 11.2 update JB???!!!
Yes, soon.
Thanks you so much sir…
Watch day iOS 11.2 JB possibles?????
It will take months.
hopefully waiting for iOS 11.2.2 #JB. soon as possible
i appreciate your team and effort
Thanks in advance
Welcome, Yash.
Hi I m happy to hear about this. Hope this turn into Electra 11.2.2 jailbreak or new jailbreak, I m on it sitting all day on 11.2.2..
hopefully waiting for iOS 11.2.2 #JB. soon as possible
i appreciate your team and effort
Thanks in advance
If a jailbreak can’t be discovered out of this vulnerability then hopefully we will get a Nonceset that will allow users who saved their shsh blobs to downgrade. I would be happy with just that.
We need a kernel exploit for that so it will still take some time.
Won’t happen, that would require a kernel exploit and this is only a bluetooth vulnerability
Hi I m happy to hear about this. Hope this turn into Electra 11.2 jailbreak or new jailbreak, I m on it sitting all day on 11.2
Great! A new jailbreak will hopefully be released very soon.
I know you guys are trying very hard on iOS 11.2.x jailbreak. Keep going
#JAILBREAKER AND DEVELOPERS ROCK
They are a security research team and won’t release a jailbreak tool for us. But this can allow other developers to expand on their work and build tools based on it.