While jailbreakers are focused on iOS 11.1.2, some hackers are working quietly on iOS 11.2. Here’s a new sandbox escape IPA file released for iOS 11.2-11.2.2.
Table of Contents
What is UnjailME?
UnjailME is a proof of concept sandbox escape tool for iOS 10-11.2.5. It is developed by Sem Voigtländer, the lead security researcher of Coffeebreakerz.
This tool utilizes the Bluetooth vulnerability released yesterday by Rani Idan of Zimperium zLabs. Here are a few of its features –
- FTP access (sandboxed)
- Sandbox escape proof of concept
- User interface
Surprisingly, Apple patched Idan’s vulnerability in iOS 11.2.5 firmware.
Despite Apple’s patch, unjailme still supports that version which speaks volumes about Sem’s hacking capabilities.
- Warning – Do not try this tool if you are not a developer or power user. It will not harm your device but it’s useless for the average user in its present form.
Is it an iOS 11.2-11.2.5 jailbreak?
Since unjailme is based on Zimperium’s exploit, it can only escape the sandbox restrictions imposed by iOS.
Powerful features such as root access, remounting the filesystem, setting nonce, etc are unavailable as of yet.
Although it’s a not a full jailbreak, it can potentially become the next v0rtex injector. The upcoming versions of this tool will include the following features –
- Unsandboxed FTP access (planned)
- Remote SSH access with dropbear client (planned)
- Springboard code injection
- launchd daemon
Download UnjailME
- IPA file (alpha version)
Requirements
- iPhone, iPad, or iPod touch
- iOS 10-11.2.5 firmware
- A computer running Windows, macOS, or Linux
- Cydia Impactor
- Internet connection
- FTP client
How to use UnjailME on iOS 11.2-11.2.2
Install the IPA file
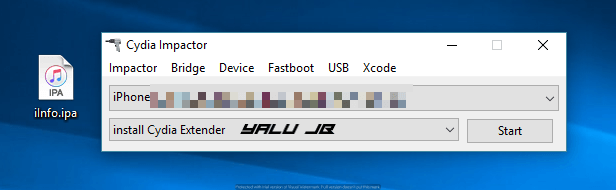
Step 1 Launch Cydia Impactor.
Step 2 Download the UnjailME IPA file using the link above.
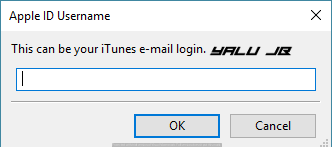
Step 3 Sideload it on your device by dragging it onto Cydia Impactor’s window. Once it prompts you to enter your credentials, type in your Apple ID username and password.
Step 4 Wait for it to install the app on your device. Once the app is on your home screen, go to Settings > General > Profiles and Device Management and trust this app under your Apple ID.
Trigger the vulnerability
Step 5 Launch the proof of concept application from your home screen.
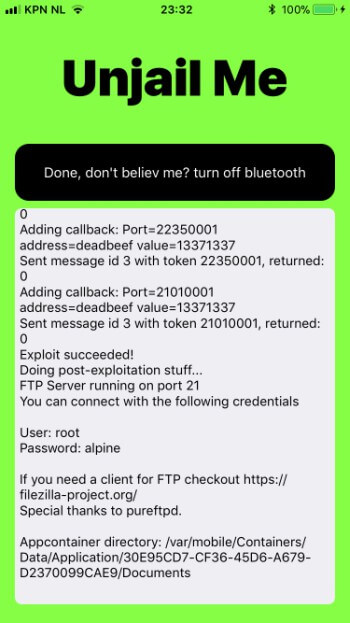
Step 6 Enable Bluetooth from the Control Center. This step is essential because this proof of concept relies on the “bluetoothd” daemon.
Step 7 Press escape sandbox to trigger the vulnerability. Wait and let it complete the exploitation.
Step 8 Use the in-app FTP credentials and connect to WinSCP from your computer. Alternatively, you can start an FTP session on-device using App Store applications such as FTPManager and Documents by Readdle.
Step 9 You can remotely browse the files present in the UnjailME directory using FTP protocol.
Uninstallation
Step 10 Turn off Bluetooth from the Control Center.
Step 11 Delete the application.
Step 12 Restart your device.
The developer intends to release a more powerful version in the near future. He has already set the stage for a full-fledged iOS 11.2.5 jailbreak.
If you want to support him, you can donate to him via Paypal to support his security research.
For more jailbreak tools and downloads, follow us on Twitter and Facebook.





work on 11.2.5?
Yes, the latest version does.
11.2.6?
Yes.
I have iPhone SE on iOS 11.2.5 and when I tap on “Escape Sandbox”, it doesn’t do anything. After a minute or two it just crashes with no output. Are you sure it works on iOS 11.2.5 ?!
Yes, it does according to the developer.
I test unjail me, but I have a problem, when Open filezilla o cyberduck connect tje iphone with the Ip 192.168.1.xx, connect OK, but the folders are emty, I can not view the archives,
You can’t view your device’s filesystem with it, only the UnjailME directory.
then it is necessary to wait to future versions, To have full access to the root files.
Yes, that’s right but that won’t be happening with this exploit alone.
How to Fix Error 3194
i cant restore to 11.2.5 from 11.2.6 Iphone6S Plus
Please Help
That’s because it’s no longer signed.
I cant restore to 11.2.5 from 11.2.6 Iphone6sPlus
Error 3149
Please Help
Is Apple still signing ios 11.2.5.
I tried restoring but getting error
No, they are not.
So does it work on iOS 11.2.5 ?
Yes, it does.
It‘s Not work iPhone 6s iOS 11.2.5
It does work.
Can you elaborate. How come it works for you and not on my iPhone SE ios 11.2.5 !?
Are you using Wifi?
Very good very fast beginning. I’m very happy a lot of love to all people’s helping
Pleas help my iPad is in a restart loop because I deleted /usr/???/boot?? Trying to get stupid Electra to work I hve shsh blobs saved I don’t think I have find my iPhone but I don’t want to upgrade helpppppp ios11.1.2
Try using Reiboot or FutureRestore but I don’t think it will work. Only a proper restore with iTunes will work now.
So I am forced to update
yes, but try the alternatives that I listed above.
Find my iPhone iOS on can I reset it from there
Can I use reset on find my iPhone
Yes, you can use that.
So no update?
Yes, no updating.
I’m doing it nope it needs to connect to internet
You just need a Wifi connection for that.
No th iPad needs internet to reset it haset got at umil ttturns I but it won’t
I guess your only option is to upgrade via iTunes.
Put your phone into dfu mode the use future restore tool with saved blobs
But don I need to
Nounce set for that
Can you giv me a tutorial