An eminent security researcher from Massachusetts Institute of Technology recently discovered a new vulnerability that affects APT, the package manager, upon which Cydia is based. Does this bug affect Cydia? Let’s find out below.
Table of Contents
Linux systems are vulnerable to man-in-the-middle attacks
CVE-2019-3462 vulnerability leaves systems using APT susceptible to network man-in-the-middle and mirror package attacks. It allows the attacker to execute arbitrary code with administrator access on affected devices.
Max Justicz, a security researcher from the blockchain startup Algorand, was the first to discover this vulnerability. He published his findings on his personal blog here.
For the uninitiated, APT (Advanced Package Tool) is a package manager for Debian, Ubuntu, and Linux systems.
Cydia, the mainstay jailbreak package manager, is nothing but a graphical front-end for APT.
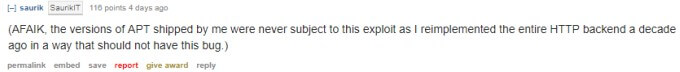
Remote Code Execution Vulnerability (CVE-2019-3462) in apt/apt-get. Cydia is not subject to this bug. #Debian #security pic.twitter.com/ZTJifkuuGw
— Yalu Jailbreak (@Yalujb) January 27, 2019
For this exploit to work, the attacker must perform the following actions –
- Monitor a public network
- Check the devices that are jailbroken (or using APT)
- Wait for the victim to transfer a package via APT.
- Send a malicious package to the any of the default sources.
Is Cydia vulnerable to CVE-2019-3462?
Since Cydia is based on APT, it should be vulnerable to CVE-2019-3462 in theory. That, however, is not the case here.
According to Jay Freeman aka Saurik, Cydia is not subject to this vulnerability primarily because of the method of implementation followed ensures the backend stays insusceptible to such attacks.
Here’s one caveat, though – unc0ver jailbreak for iOS 11 doesn’t use Saurik’s version of the HTTP Backend, instead it relies on the one developed by Sam Binger, Jay Walker, and Kirb.
According to Kirb, the unc0ver Development Team ported Saurik’s CFNetwork logic to iOS 11. So, the version of APT used in unc0ver is based on Saurik’s APT builds.
As far as Electra jailbreak is concerned, it relies on the HTTP Backend developed originally by Saurik.
CVE-2019-3462 patched in latest APT build
This bug has been fixed in the latest versions of APT. If you are still using an older APT, avoid using it in public networks, which are often open to man-in-the-middle attacks.
Even if Cydia were vulnerable, the attack would have required a lot of effort since the attack vector pertaining to this bug is rather small.
If you have a jailbroken device, you’ve got nothing to worry about.

![5 New Features we would like to see in iOS 11 [My Wishlist] 5 New Features we would like to see in iOS 11 [My Wishlist]](https://cdn.yalujailbreak.net/wp-content/uploads/2017/06/ios11wishlist-1-211x150.jpg)