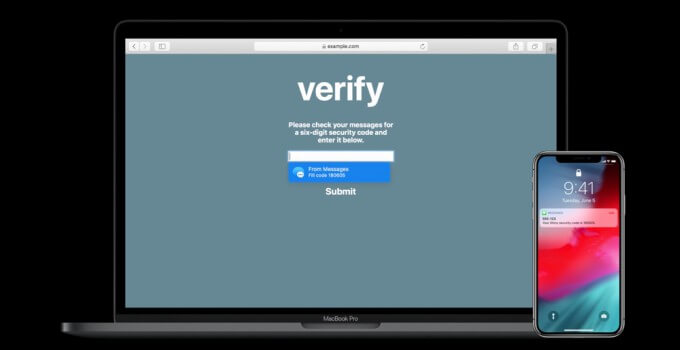
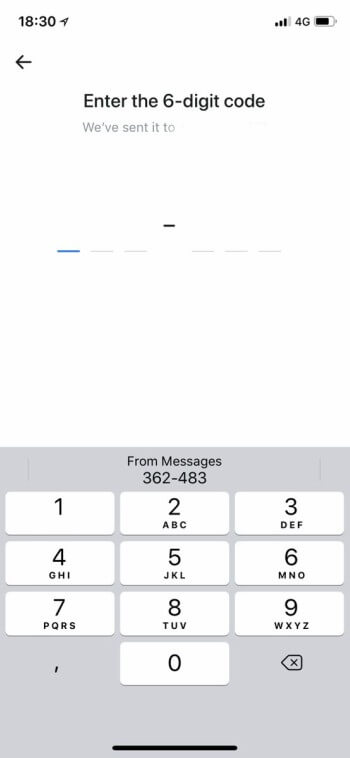
iOS 12 simplifies two-factor authentication by automatically inserting security codes in the required fields. However, security researchers have expressed concerns over the safety of this new feature.
Table of Contents
2FA may leave your device open to security threats
iOS 12 and macOS Mojave automatically enter 2FA security code received through SMS. This negates the need to memorize the one-time code or check your messages.
Andreas Guttman, a security researcher from OneSpan, argues that this new technology exposes users to online banking fraud.
According to Guttman, transaction authentication relies on the correctness of the action, not just the identity of the user.
This gives rise to security issues because iOS 12 automatically extracts the OTP. It is unable to differentiate between an OTP belonging to a 2FA and TAN (Transaction Authentication Number).
The user is presented with the required code without the accompanying transaction data.
User verification of the transaction message is precisely what ensures the security of this two-factor authentication process. Taking this part out of the equation reduces the effectiveness of 2FA.
Moreover, it also leaves the user open to Man-in-the-Middle attacks while using Safari or when a malicious website or app gains accesses to the user’s banking service.
Our take
Gutmann’s hypothesis, with all due respect, is unfounded because the security code autofill still relies on user intervention.
A device on iOS 12 will not automatically fill in the code unless the user taps and confirms it.
The security researcher’s theory uses a hypothetical malicious website as a basis. However, even a malicious one-time authorization password will still require user interaction.
Security Code Autofill might become a problem in the future once a proof-of-concept exploit goes public.
But until that happens, you can continue using this feature without worrying about security.
[Source – Vasco.com]