FBI and other government agencies often use unethical methods to hack into Apple devices. Here’s how they unlock any iPhone with GrayKey unlock box.
Table of Contents
GrayKey is capable of unlocking any iPhone
Shady security company Grayshift has developed an iPhone unlocking tool called GrayKey. The box sports an overtly simple design with no fancy buttons and display units.
Although it looks like a simple modem-like harmless device at the outset, it can crack your iPhone’s passcode with ease.
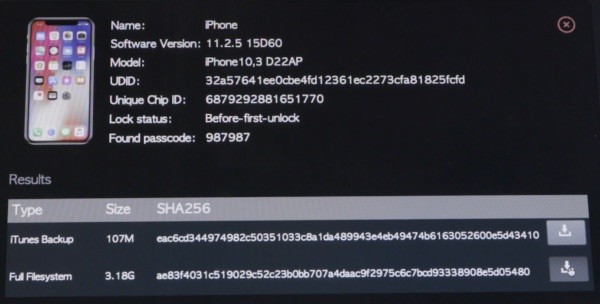
GrayKey can hack into any Apple device running the latest iOS operating system, iOS 11.2.6.
Even the iPhone X, the most secure smartphone by Apple to date, is not immune to this mysterious hacking box.
The GrayKey unlock box comprises two Lightning ports, with which the user can use to crack two iPhone devices simultaneously.
Grayshift provides absolutely no details regarding this tool on its official website. Its official website consists of a simple login and signup page for its clients.
How does GrayKey unlock the iPhone?
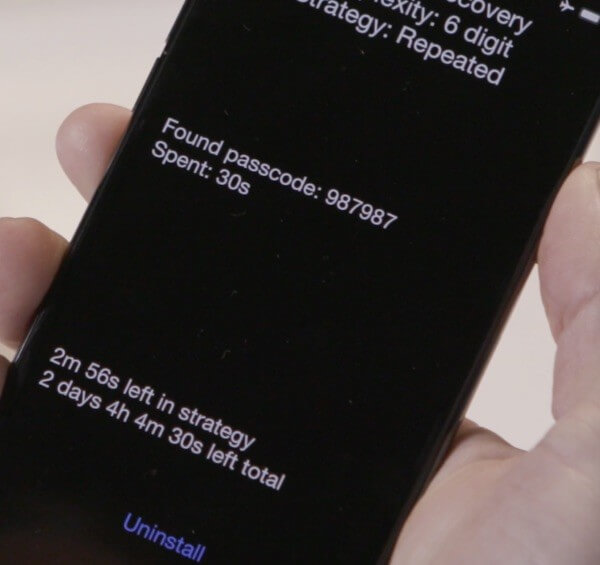
- User connects the target device to the box.
- Once a connection is established, the box installs a special hacking software on the target device.
- The passcode cracking process now begins. It can take up to a few seconds or a few days depending on the complexity of the passcode.
- User can now download any data on the device and also access its passcode.
Hackers and government agencies can also use GrayKey to remotely unlock any iPhone. The remote process works through Grayshift’s website with the help of Geofencing technique.
How can you protect your iPhone?
Unfortunately, there’s no surefire method or tool that you can use to mitigate this threat.
Since this tool requires physical access, ensuring that your device stays in the right hands is crucial.
If you are an average user, you should worry about it much. This tool costs $15,000 for remote cracking sessions and $30,000 for the physical method.
Its high price, however, won’t keep unofficial iPhone repair shops and unruly individuals from stealing user data.
I suggest using authorized service centers whenever possible and sticking to trusted sources for repairs and replacements.
For more security news and updates, follow us on Twitter and Facebook.




from the available information, which is admittedly not much, it would seem as though they have found a flaw in the Secure Boot chain, or some other similar low-level loading stage that allows them to run their own unsigned code, possibly a ramdisk, perhaps a 0-day exploit. Either that or they’ve acquired bootloader/fw signing certs, but that sounds very unlikely given Apple’s stance on the matter.
True that. Some rat seems to be leaking stuff from the inside. They can’t break security for all latest versions and devices.
In fact there Is this kind tool before the GreyKey, which use a flaw in DFU to brute-force the password. But that device doesn’t work with newer iPhones.
Was it developed by Cellebrite?
Wish I could afford this. My daughter died and I want the pics off her old iPhone 6.