I am back with another interview and this time our guest is none other than the lead developer of Coffeebreakerz. Read the full conversation below.
Today, I will be talking to Sem Voigtländer, a talented young hacker from the Netherlands. He is the leading developer of Coffeebreakerz, an iOS hacking Dev Team.
Table of Contents
Q1. How and when did you get started with jailbreak tweak development?
A. I never started developing jailbreak tweaks, it’s because I do not like putting a lot of time in work that can be only be used while jailbroken.
I’ve been studying security since I was 13. My passion started after I watched the matrix.
Since I knew already some programming languages and in basics how iOS works, I wanted to see if I could create a jailbreak as well. This was about two years ago now.
So after a long way of learning, I understand the kernel, it’s drivers and the operating system.
But writing a jailbreak requires a lot of knowledge so I started learning about binary exploitation techniques like –
- Use After Free vulnerabilities
- Buffer overflows
- Type confusion
I practiced them by playing CTF challenges. And that’s how I started the real research on iOS Security.
Q2. CheekiJailbreeki combines ziVA and triple_fetch exploit into a jailbreak. Can it be used to install Cydia on iOS 10.2.1?
A. That’s the goal of the repository.
CheekiJailbreeki is unfinished. But if a few symbol issues in ziVA exploit are fixed and Yalu’s patches for iOS 10.2, as they are the same for iOS 10.2.1, are added the jailbreak could work.
I do not think it will work for iPhone 7 devices but at least it will do for the rest of the 64-bit devices.
I do know very little about KPP but Coolstar came with an idea –
- Patch as many things in userland as possible.
- Patch and unpatch the rootfs in the kernel.
- Prevent KPP from being triggered.
I’m still skeptical about this though. I do not think we will see an iOS 10.2.1 jailbreak for iPhone 7 users this year.
Q3. Although you have quite a few contributions under your belt, the community has a hard time trusting the Coffeebreakerz Dev Team. Are there any specific reasons behind that?
A. I think it is because I am working while I am learning.
I make mistakes by thinking that some things will work, overlooking some security policies or just understand some of them a bit wrongly.
I think it’s okay to make mistakes. But indeed people will have doubts about the trustworthiness of you then.
Q4. Which projects are you working on right now?
A. Mainly MTJailed, as I froze the work on the jailbreak. I got bored, do not own a device on iOS 10.2.1 and also do not like to be jailbroken on my main device.
Besides, I have put all the work needed for a jailbreak together and there are little steps to be done. I think the community should finish it whether they can or not.
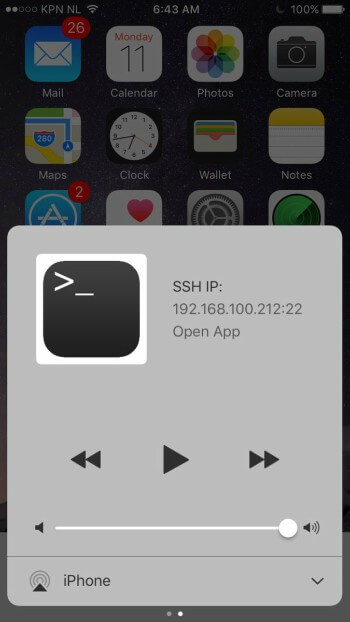
MTJailed basically is a Terminal for non-jailbroken devices. It is meant to run inside the sandbox but has as much usability as a terminal on a jailbroken device.
- It functions by using reverse-engineered private API’s and making use of Apple’s unprotected parts of the sandbox.
- It has a server for executing commands remotely, like SSH and a server for transferring and managing files.
So my real goal is to make it just as convenient as a jailbroken terminal.
Q5. Do you own a jailbroken device? What are your favorite Cydia tweaks and App Store apps?
A. I have a jailbroken device, an iPhone 4S on iOS 6.1.3.
My favorite tweaks, to be honest, are –
- MTerminal
- Python
- GCC
- OpenSSH
- Veency
I don’t know if that can be seen as tweaks, they are more like software packages.
A cool tweak I know from iOS 6 that I love very much is TVLock. It’s a tweak that zips your screen when you lock it. Just like when you turn off an old TV.
Q6. iPhone X and iOS 11 will be very hard to jailbreak. What’s your take on that?
A. It’s time for the public to find alternatives, like my MTJailed for example.
If we all think outside the box the possibilities will still be big enough to extend the iOS operating systems capabilities without touching security.
But even when Apple makes security stronger by improving SEP and AMCC and the Operating System, there will always be bugs that can be used for breaking security. Because people make mistakes.
The point is the exploits for this upgraded secure system will be of high value and therefore most likely not see the public but will be sold to, for example, Zerodium.
Q7. What can the jailbreak community expect from you in the future?
A. I will be focusing on solutions to extend non-jailbroken iOS capabilities like MTJailed.
I might be working on the 10.2.1 jailbreak if the community doesn’t finish it this year, but in the future, I will not be working this actively on jailbreaks.
I will be continuing my research on iOS and post a tweet or an article every now and then.
Like, for example, about the Nesstool app that I reverse engineered and found guilty to using spying on people.
Nesstool is malware. It does not only log and manage your internet traffic, but also collects private info. Conclusion: It is spyware.
— MTJailed (Terminal) (@MTJailed) September 19, 2017
That’s it for now, folks! Be sure to follow the official Twitter handle of Coffeebreakerz Dev Team for the latest updates.
Also watch out for Sem’s latest tool, MTJailed, which he will be releasing very soon.
If you liked this interview, don’t forget to follow us on Twitter and Facebook.