Ever since axi0mX dropped the unpatchable checkm8 BootROM exploit, the chatter hasn’t subsided. Each one of us yearns for a permanent jailbreak, but this exploit is capable of a lot more than that. Read the complete FAQ below and see for yourself what you can and can’t do with this exploit.
Table of Contents
Q. What can the checkm8 BootROM exploit do?
- Jailbreak the latest signed firmware version as long as you have a vulnerable device.
- Tethered downgrades without SHSH Blobs to any compatible version. However, in doing so, you will encounter issues with the SEP (Secure Enclave Processor). Any feature that depends on SEP will simply not work.
- Flash a Custom Firmware (CFW) for jailbreaking and activating your Apple device, adding a custom boot logo or verbose boot.
- Dump SecureROM for security research.
- Dual-boot two different operating system versions on the same device.
- Load an SSH ramdisk.
- Port and boot experimental builds of Android and possibly even Linux operating system.
- Bypass KPP/KTRR, AMFI, CoreTrust, and other security features.
- Patch all security features present in any operating system update.
- Demote device to enable JTAG
- Boot device
- Send file to device in DFU Mode
- install alloc8 exploit to NOR
- USB exploit for pwned DFU Mode
- Dump memory to stdout
- Hexdump memory to stdout
- Dump NOR to file
- Flash NOR (header and firmware only) from file
- Install 24Kpwn exploit to NOR
- Remove 24Kpwn exploit from NOR
- Remove alloc8 exploit to NOR
- AES decrypt with GID key
- AES encrypt with GID key
- AES decrypt with UID key
- AES decrypt with UID key
Q. Is checkm8 tethered or untethered?
Unlike older exploits like limera1n and SHAtter, checkm8 is tethered, not untethered.
This means all jailbreak and downgrade tools that rely on checkm8 will be tethered or semi-tethered, meaning you will need to execute ipwndfu on the computer while your device is in DFU mode each time you wish to put it in jailbreak mode.
If you reboot your device, it will boot to the non-jailbroken state (stock operating system) just fine, rootlessJB developer Jake James confirmed in a recent tweet.
why are people still ignorant about this. a tethered exploit is enough for a semi-tethered jailbreak, don't panic people. you'll be able to reboot just fine in stock mode. https://t.co/JE4qI7GIvx
— Jake James (@Jakeashacks) September 28, 2019
You will still be able to use the stock operating system without any difficulty even if your iPhone or iPad dies and you can’t access your computer or laptop.
Q. Which devices are compatible?
Currently, only the following devices are compatible –
- s5l8947x – Apple TV 3rd-generation
- s5l8950x – iPhone 5, iPhone 5C
- s5l8955x – iPad 4th-generation
- s5l8960x – iPad Air, iPhone 5S, iPad mini 2, iPad mini 3
- t8002 – Apple Watch 1, Apple Watch 2
- t8004 – Apple Watch 3
- t8010 – iPad 6th/7th-generation, iPhone 7, iPhone 7 Plus, iPod Touch 7th-generation
- t8011 – iPad Pro (10.5-inch), iPad Pro (12.9-inch) 2nd-generation, Apple TV 4k
- t8015 – iPhone 8/8 Plus, iPhone X
Developers plan to release future versions with support for the following devices –
- s5l8940x/s5l8942x – iPad 2nd Gen, iPhone 4S, iPod Touch 5th Gen, iPad Mini
- s5l8945x – iPad 3rd-generation
- t7000 – iPad Mini 4, iPhone 6/6 Plus, iPod Touch 6th-generation, Apple TV 4
- t7001 – iPad Air 2
- s7002 – Apple Watch 1st-generation
- s8000 – iPad 5th-generation, iPhone 6S/6S Plus, iPhone SE
- s8001 – iPad Pro (12.9-inch), iPad Pro (9.7-inch)
- s8003 – iPhone 6S/6S Plus, iPhone SE
Q. Can this exploit lead to an untethered jailbreak?
Unfortunately, any user-facing jailbreak tool based on this exploit will never be untethered.
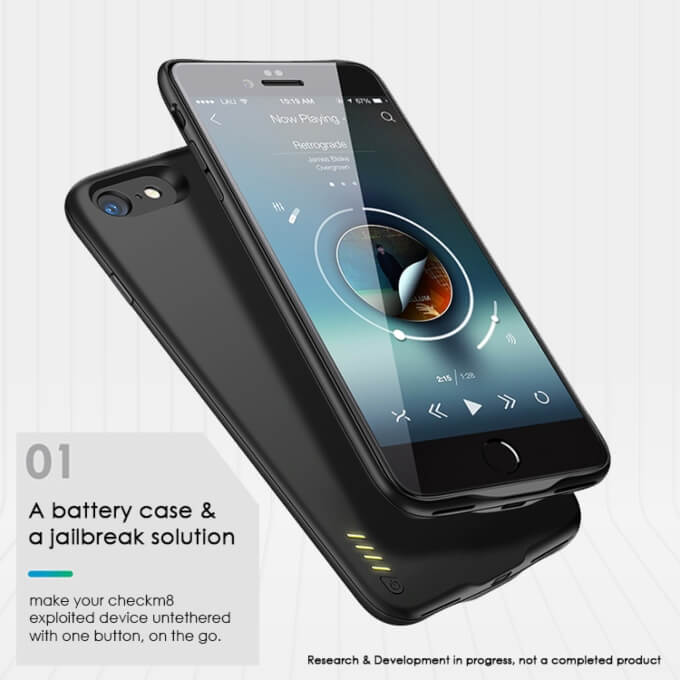
Nevertheless, we could hardcode a script into a Raspberry Pi Zero that can automatically load checkm8 or use a special battery case that can keep the device in jailbreak mode at all times.
Installer developer Sammy Guichelaar is in talks with a Chinese manufacturer for the production of a “untether” case.
I’m in talks with a chinese case maker, their minimum order quantity per device type is 250 cases. They’re saying if we provide them the hardware, provided it is small enough they can make the case work just fine. It’d be both a battery case & untether case.
— Sammy Guichelaar (@SammyGuichelaar) September 27, 2019
Designed specifically for jailbreak users, the “untether” case will recharge the battery while also turning the semi-untethered jailbreak into a quasi-untethered one.
Incidentally, another enthusiast is also working on something similar called “JBCase”. JBCase is a battery case that comes with a lightning dongle that will keep your jailbreak seemingly untethered.
Once the feasibility study is conducted and the research and development phase is complete, the team behind JBCase will launch a Kickstarter crowdfunding project.
Q. Does it affect SEP (Secure Enclave Processor)?
No, this exploit does not affect the SEP (Secure Enclave Processor) at all. SEP features such as Touch ID and Face ID will stop working should you update to an incompatible firmware.
This limitation largely renders useless most of the downgrade and upgrade procedures.
Q. Can I upgrade or downgrade to any firmware without SHSH Blobs?
Yes, you can if you have a checkm8-based restore tool, but features reliant on the SEP will become dysfunctional as soon as you upgrade or downgrade your Apple device.
To ensure that Touch ID or Face ID remains functional, you must upgrade to a version that supports the latest SEP and baseband, which makes this exploit all but useless.
However, if you restore to the wrong operating system or end up in a bootloop, you could restore to another version.
For instance, if you restore to, say, iOS 11.1.2 and the restore fails somehow, you will be forced to go to the latest signed version.
With checkm8, you can just put your device into DFU mode, run the restore again and upgrade your device to iOS 12.4, which is compatible with iOS 12.4.1’s SEP and baseband.
Q. Can Apple fix this exploit?
No, checkm8 is a hardware-based bug that can’t be fixed without updating the hardware. Apple will need to release a new device with patched hardware altogether to fix this bug.
You can expect a new version of the iPhone 8/8 Plus and the iPhone X sometime soon since these are the latest devices that are vulnerable to the aforementioned exploit.
If you are interested in jailbreaking or just want to tinker around with the BootROM, now is the time to buy a new iPhone X (or any other vulnerable device).


![OSRestoreX – On-device SemiRestore for iOS 10 [DOWNLOAD] OSRestoreX – On-device SemiRestore for iOS 10 [DOWNLOAD]](https://cdn.yalujailbreak.net/wp-content/uploads/2017/03/semi-restore-1-211x150.jpg)


Hi, I tried to restore a backup on my phone with itune and it automatically downloaded the latest firmware in my phone without any warning… For now it boot on a blank page with the only option to tap home button to update…I can connect to computer in DFU mode but cant find a way to remove this downloaded update… Can I use this checkm8 to do something? I m on iphone 7 plus ios 11.3 and I think the latest version at that moment was 14.4 but its not installed yet… If I can use this exploit to do something, what would it be and how?
Thanks!
Can you tell me how to flash the Custom firmware into Iphone 4S , because I get a error 14 and need a exploit, iy you don’t mind, please tell me
You can’t flash custom firmware just yet.
I read on the iPhone Wiki that this exploit can be used to downgrade untethered to an iOS version if you have SHSH blobs. Is this true? I have some early iOS 12 and some iOS 11 SHSH blobs I might want to use.
Yes, that’s possible but still a lot of work.
can this bypass the icloud lock??
Not yet but it possibly can.
The T2 chip in all Apple Macs from 2018 is an ARMv8 t8010. The T1 is ARMv7.
Is there scope for putting T2 devices into DFU mode and reconfiguring without AST2?
This would be a huge leap forward for logic board refurbishers and repair stores.
No, MacBooks/iMacs are not vulnerable to this exploit. It only affects mobile devices and some Apple TV models.
will it be possible to downgrade my ipad mini 2 and iphone 5s devices (A7 chips) to iOS 10.3.3 without the shsh blobs. I know this was only thetered, but there is no developer (@tihmstar) who will post an update of the future restore and allow the upgrade down? or only thetered? Thank you
You can already do that but the process is very tedious.
OK, I just saw that I downloaded my shsh blobs except that I downloaded them in iOS 10.3.1. will it work? or can I only downgrade to iOS 10.3.3? and on Windows, we can not no? it’s only on Linux and Mac?
You can run it on Windows but the process is extremely cumbersome.
so I can go from iOS 12.4 to iOS 10.3.1 with my shsh blobs on Windows? I just saw your article and you said you needed a linux or mac, but you do not mention Windows. do you have a tutorial to help me downgrade to iOS 10.3.1? Thank you for helping me 😉
No, I don’t have a Windows tutorial for this at the moment.
Hey, so I’m still a bit confused on the SEP.
Right now I’m on 12.4
If this becomes a JB and the latest signed version of iOS is, say for example, 13.4 at that time… if I do a normal upgrade I will be on the latest version of iOS. I won’t be able to JB though.
So what if I upgrade the normal way and then put my phone into DFU mode and run the jailbreak? Will SEP still be broken or does this exploit itself bypass something in the SEP check at boot, which renders it unusable?
This exploit doesn’t affect the SEP at all. if you upgrade to a version with an SEP and baseband that’s compatible with the latest signed version at that point in time, you will be fine.
so does jailbreaking with this exploit depends on computer like taig JB for ios 8?
or it can be like Un0cover?
It will have to be run from the PC like limera1n.