Hacker 08Tc3wBB recently teased a new unconventional exploit for the iOS 13.6.1 operating system. Could this exploit lead to an iOS 13.6.1 jailbreak? Let’s find out below.
Table of Contents
08Tc3wBB Unconventional exploit for iOS 13.6.1
08Tc3wBB recently demonstrated a new unconventional exploit for the iOS 13.6.1 operating system. This exploit is unconventional in the sense that it doesn’t try to obtain the kernel’s task port.
Up until now, jailbreak exploits have relied on grabbing the kernel’s task port, also called tfp0. This allows us to acquire arbitrary read/write privileges pertaining to the kernel – the core of the iOS operating system.
Arbitrary read/write privileges allow the attacker to add custom code to the kernel. This, in turn, grants the attacker unrestricted access to the system or, in other words, lets you jailbreak your Apple device.
This new exploit is not a groundbreaking development, it’s just a different approach to obtain the same kernel read/write privileges.
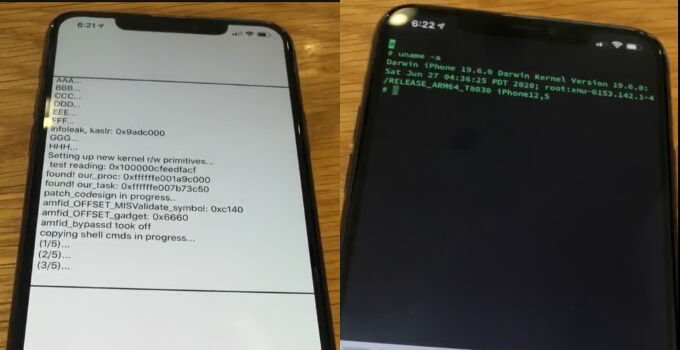
Here’s the video security researcher 08Tc3wBB posted on his Twitter handle.
iOS 13.6.1, iPhone 11 Pro Max, using custom built kernel read/write primitives, completely got rid of the tfp0 method. I’ll make it public when it’s appropriate. #JAILBREAK pic.twitter.com/3mwIVsrN1s
— 08Tc3wBB (@08Tc3wBB) August 15, 2020
In this video, the hacker is seen navigating to the “Software Update” section of the Settings app to show the operating system to the readers.
He then launches the “ios13_6_ap” application to kickstart the exploitation process. Once the device is pwned, a local SSH connection is established using the Termius app.
08Tc3wBB also plans to make the exploit public when the time is right.
Once the exploit goes public, pwn20wnd and other development teams could incorporate this exploit in a user-facing jailbreak like unc0ver and Odyssey.
Could this exploit lead to an iOS 13.6.1 jailbreak?
As far as credibility goes, 08Tc3wBB is a trusted security researcher who is followed by renowned developers like pwn20wnd and Luca Todesco.
Furthermore, researcher axi0mX of checkm8 fame retweeted the aforementioned tweet.
It’s worth noting that we can’t use every new exploit that surfaces online to develop a jailbreak. At the outset, this exploit seems powerful enough to build a jailbreak.
But, we can safely assume that this exploit will not go public anytime soon.
Since Apple is yet to patch the exploit, 08Tc3wBB might try to hold onto it in case it works on the iOS 14 operating system.
Nevertheless, if you are interested in a “future jailbreak”, we recommend staying on iOS 13.6 firmware.
The reason being that iOS 13.6.1 has no new CVE changes, which implies that there’s no significant difference between iOS 13.6 and iOS 13.6.1.
All in all, this “unconventional” exploit could lead to an iOS 13.6.1 jailbreak in the future.
For more jailbreaking news and updates, be sure to give us a thumbs up on Facebook and Twitter.